Ransomware attacks are skyrocketing
According to antivirus firm Sophos 48% of UK organisations have been hit by ransomware attacks in the last year. Trend Micro’s 2019 ransomware report also indicates that ransomware activity is on the rise, with over 40 million ransomware “detections” made between January and April 2019 – compared to just over 50 million for all of 2018.
It’s estimated that 13 percent of schools have experienced ransomware attacks, making education one of the sectors most often targeted by hackers. Around a third (33%) of UK universities have been targeted with ransomware, freedom of information (FOI) requests submitted by the agency TopLine Comms have revealed.

The education sector presents a tempting target to ransomware gangsters for several reasons.
- Students often engage in risky online behaviours that expose them to ransomware attacks, such as treating email attachments without appropriate wariness, and visiting websites trafficking in pirated entertainment.
- The highly open and interconnected nature of campuses opens multiple points of possible malware infiltration: find a weak link, and ransomware can spread quickly from student to faculty to staff PCs and servers.
- Cost pressures have made it difficult for some institutions to fund IT security investments. Unfortunately, the education sector tends to lag well behind industries like finance, retail, and healthcare with regards to the resilience of its tech infrastructure.
This combination of factors makes the education sector one of the most popular targets for ransomware attacks.
And when you combine the above with the fact that schools have minimal defence mechanisms and hold significant amounts of sensitive student data, they become the low-hanging fruit of cyberattack targets.
What is Ransomeware?
Ransomware is a type of malicious software that infects computer servers, desktops, laptops, tablets and smartphones, infiltrating through a variety of mechanisms and often spreading laterally across a campus from one device to another. Once it infects a system, the virus quietly encrypts every data file it finds, ultimately displaying a ransom note to the user. The extortion message starts by demanding an online payment of anywhere from hundreds to thousands of pounds, often in some untraceable cryptocurrency such as Bitcoin in return for the decryption keys needed to restore the user’s locked files. The demand often includes a series of deadlines for payment, with each missed deadline leading to higher ransom demands and perhaps some destroyed files. If the victim doesn’t pay, the attacker discards the decryption keys, making the data permanently inaccessible.Over the past couple of years, this scenario has played out many times and hardly a week goes by without news of another successful ransomware attack on an educational institution.
Here are just a few:
- University College London was a famous victim of the WannaCry ransomware epidemic that swept through 100,000 systems worldwide over a single weekend in 2017, losing access to its shared data repositories and student management system.
- Los Angeles Valley College paid over $28,000 to online criminals in the wake of a ransomware attack that brought down its websites, email servers and voicemail systems.
- The University of Calgary was paralysed for over a week by a ransomware attack, eventually paying a $20,000 ransom to restore over 100 of its systems.
- Over 3200 PCs were laid low by a ransomware attack on Carleton University, which eventually paid $35,000 to restore them.
More recently, at least 10 universities in the UK, US and Canada have had student / alumni data stolen after hackers targeted Blackbaud, one of the world’s largest providers of education administration, fundraising, and financial management software.
The UK institutions confirmed by the BBC that have been affected are:
- University of York
- Oxford Brookes University
- Loughborough University
- University of Leeds
- University of London
- University of Reading
- University College, Oxford
- University of Exeter
In some cases, the data compromised was limited to that of former students, who had been asked to financially support the establishments they had graduated from. But in others it extended to staff, existing students and other supporters, with data captured including phone numbers, donation history and events attended. Fortunately, credit card and other payment details do not appear to have been exposed.
Ransomware attacks are high and growing fast
These examples are just some of the higher-profile ones from recent months. Various researchers have shown that ransomware has affected a total of 55% of organisations. And the amount of ransom that criminals are successfully collecting from victims shows an alarming trend: total ransoms surged from $325mn in 2015 to more than $11.5bn in 2019. But the total damage of ransomware attacks – including the costs of operations interruption, attack recovery and forensics, damage to brand equity, and compliance violation fines – are far greater. For example, the global costs of the WannaCry attacks are estimated to total a whopping $8bn.

Impact of Covid-19
Unfortunately, the current pandemic has rapidly pushed schools into adopting a hybrid learning or mostly digital learning environment, making them considerably more vulnerable.
Firstly, they have become more accessible and easier to compromise. With the sudden thrust from brick-and-mortar to virtual, VPN etc., outside access rapidly changed from occasional use to mainstream. Most of this remote access has been from home networks and devices, leaving schools sub-optimal ways of protecting those devices. This new attack pathway enables attackers to silently access their networks and cause vast amounts of damage before the school’s security team even notices. In the time that it takes for the ransomware to be detected, the damage to bottom lines is likely to be worse and the recovery process even longer. This creates unparalleled opportunity for threat actors.
If a school’s network has been taken down due to a ransomware attack, in today’s circumstances it could very likely means that the school simply cannot function at all. This is intrinsically different than before COVID-19, where if a ransomware attack occurred, it may have caused a major disruption, but it didn’t inevitably mean that schools could not open and hold classes.
And today’s hackers aren’t hesitating to manipulate the current situation to coerce schools to pay vast sums in order to resume normalcy.
Today, in the worst-case scenario, a school could be forced to close its doors. And attackers are completely aware of the greater vulnerability that schools are in.
How educators can fight back against ransomware attacks

Educate end-users -from students to faculty
In the face of this rapidly growing threat, educational institutions can take a number of concrete steps to protect their systems from the operational disruptions and high costs of successful ransomware attacks.
Step one is to educate students, faculty and staff on the techniques that ransomware distributors use, teaching them to be wary of the email links they click on, websites they visit, and attachments they open.
Prevention through knowledge is the best way to remove the human in the cybersecurity equation. Security awareness training can be used to teach all end-users that access their network to understand how cybercrime affects an organisation and how it is committed.
Attacks will only continue to grow more sophisticated, and today’s hackers are no longer simply using straight-forward phishing schemes to entice users (although those are still prevalent). Increasingly, social media is becoming a favourite for hackers – and schools and universities are rife with students and faculty active on social networks.
As such, it is important for IT professionals and school administrators to inform end-users – students, teachers and other school officials – about methods they can use to stay safe while using campus computers, personal computers and mobile devices.
It’s critical to remember that the weakest link in any organisational cyber security defence is almost always the users.
Upgrade patches quickly and focus on systems with distributed access.

Identifying vulnerabilities early – and patching them quickly – is another key to good security hygiene. Unfortunately, schools with smaller budgets and IT teams do not have the resources to keep up with constant patch cycles. That is probably one of the reasons the aforementioned WannaCry attack was able to get through. Schools can help prevent such malware attacks from working by ensuring that their applications are up to date, with any updates and patches being regularly and quickly implemented.
Adopting a scheduled patch upgrade programme by setting aside one day out of the week to ensure that all systems are up to date with the latest security measures is an easy way to help keep networks safe. Network administrators should do this continuously, making it a part of their weekly IT routines. Adopting such a process also makes it much easier to push out patches and implement and test updates to ensure they do not adversely impact schools’ IT infrastructures.
Implement modern security solutions
IT now plays an integral part of a modern education, with much depending on complicated forms of hardware and software. Without the right protection, one virus or Trojan horse could cause massive damage to a school network.
However, a network firewall can keep your school safe and running without interruption.
A school’s IT network is like any large and diverse network; it’s intricate, connected, and has a lot of access points. Without a robust firewall, it is vulnerable and will be attacked.
Repairs become necessary, making both time and money add up. Time taken out of the school day and the students’ education. Money taken out of the budget that could improve school facilities. In short, putting a network firewall in place saves money on your school budget and makes running the school day more efficient.
Moreover, from a hacker’s perspective, schools today are currently at their most vulnerable. Due to the pandemic, many of these organisations have rapidly moved online, and no longer have full protection in place. Indeed, as schools and universities increase their reliance on remote connection and access for teachers and students alike, they are also inadvertently expanding their threat surface by providing attackers with many more touch points which attackers can manipulate to gain access.
Having adequate firewall and endpoint protection systems in place is crucial. Unlike the corporate environment that may have the budget to spend on products and a large security operations centre (SOC) team, schools should be focused on having cybersecurity solutions that prevent the widest possible range of attacks. There simply aren’t the time or resources available to investigate every incident that occurs. And endpoint protection can be configured to prevent attacks from the outset.
Invest in Security Information and Event Management (SIEM)
Ongoing monitoring and system management are critical to maintaining a solid security profile, and SIEM tools allow IT managers to do this with ease.
SIEM helps managers ascertain a baseline analysis of their operating environment, making it much easier to detect anomalies later. They also gain visibility into virtually all aspects of network activity and receive alerts when a potential threat is flagged. These alerts help pinpoint the cause of the problem and allow for quick remediation of nascent attacks before they adversely impact the network.
Modernise legacy IT systems
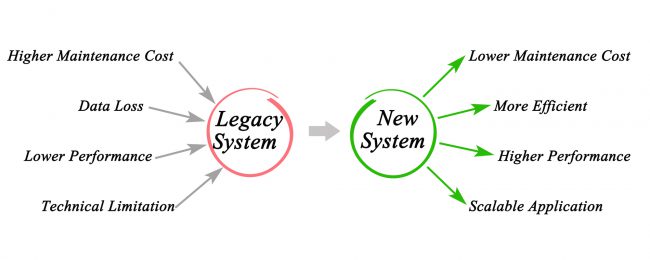
Cyberattackers use cutting edge technologies and methods to exploit university systems that are, in some cases, woefully outdated and outmatched. Legacy IT systems can be highly susceptible to hackers and ransomware because they are difficult or impossible to patch. An older system like Windows XP, for example, is much more likely to be infected with malware than newer versions of Microsoft’s operating system.
Although many schools are operating on very tight budgets, they need to allocate at least some funds for modernising legacy IT systems. Long-run savings will ultimately outweigh the initial investment, and a school’s security posture will improve dramatically.
The main point of focus for ransomware is to target a network, replicate itself and cripple the organisation. Remote learning provides the perfect opportunity for threat actors to install trojans and malware on machines being used by students and teachers that are not owned or protected by the school.
Good network and security hygiene measures remain highly important, including measures such as segmenting networks to make it harder for ransomware to spread from system to system, keeping endpoint anti-malware software up-to-date, and patching known vulnerabilities in operating systems and applications as quickly as possible.
Have a back-up plan in place
Scheduling regular file backups – ideally, at least once a day – can be a lifeline for organisations hit with a ransomware attack. It is imperative to institute a rigorous backup regimen and keep multiple copies of critical data both locally, off-campus, and in the cloud. Routine, frequent backup remains the most fool proof defence against ransomware: if your systems are compromised, you can simply identify the onset of the attack and restore your systems from clean backups created before the incursion. However, backing up alone is not enough.
Managers must test the restores of their backups to ensure they are working properly. Many people routinely make the mistake of not testing, only to find out that their files are not restorable when they need them the most.
In addition, backups should be stored offline and preferably offsite. Online backups can be too easily subject to the same risks as the original files, and distance from the main data centre provides an extra level of security.
And as more and more educational establishments are using Cloud applications as teaching aids, schools need to ensure that cloud security measures are in place to guarantee that both security and privacy of personal data is being upheld. Make sure your Cloud provider has robust security in place and ticks the boxes of the General Data Protection Regulation (GDPR) where required. Always choose a Cloud provider that puts security first.
Conclusion
To avoid becoming victims of the next widespread ransomware attack, educational institutions will have to deploy the basic measures outlined above, and consider deploying leading-edge technologies for ransomware defence that uses machine learning to identify ransomware attacks in progress, instantly terminate them, and automatically restore any damaged files.
Most schools and universities have limited time to research ransomware mitigation solutions and don’t have the proper IT resources in place to address ransomware threats. MSPs can assist by handling heavy lifting around ransomware protection, education, implementation and setup. Most importantly, they can help schools establish the best countermeasures – antivirus, endpoint security, and great backup and recovery solutions.
Syscomm is a Managed IT Services company and has been providing high end network solutions to the education sector across the UK for over 15 years. Our network solutions connect Clouds, applications, users, staff, customers, multiple types of devices and their data, while securing them from today’s increasingly threatening environment. A new era of business demands the next generation of network.
Learn more about how we can help your school or Multi Site Academy...
Talk to one of our cybersecurity
and network specialists today
0247 771 2000